Cloud adoption promised control: faster deployments, scalable resources, and infrastructure that could be provisioned on demand.
What it delivered in practice, for many organizations, is a different problem. The faster teams can change infrastructure, the harder it becomes to ensure those changes are safe, compliant, and cost-controlled.
Infrastructure misconfigurations are among the leading causes of cloud security incidents, unplanned outages, and unexpected cost overruns. Despite that, most organizations still govern infrastructure changes with far less rigor than they apply to application deployments. That gap is where operational risk lives.
The shift to infrastructure as code changed the stakes
With tools like Terraform or OpenTofu, an engineer can provision a complete cloud environment in minutes. Network rules, access policies, database configurations, and compute resources are all defined in code that can be modified and applied with a single command. That speed is genuinely valuable. The problem is that governance processes designed for slow infrastructure change haven’t kept pace with it.
When infrastructure moves at the speed of code, mistakes reach production just as fast. Most engineering teams haven’t built an equivalent of a review-and-testing pipeline for infrastructure changes. Changes get applied and discovered to be wrong only when something breaks.
What ungoverned infrastructure change actually costs
The consequences fall into three categories. Security and compliance exposure is the most visible: a misconfigured storage bucket, an overly permissive IAM policy, or an open database security group can each create serious vulnerabilities and, in regulated industries, compliance failures with real legal consequences.
Operational instability shows up as downtime. A load balancer modification that breaks a dependency, a network rule change that cuts off a service, a scaling policy that causes resource exhaustion under load. These incidents typically trace back to changes that weren’t validated before being deployed to production.
Cost overruns surface more slowly. Untagged resources that bypass chargeback allocation, compute provisioned without sensible limits, and storage tiers changed without lifecycle rules in place. Cloud bills don’t lie, but they do take time to surface.
Guardrails as the practical answer
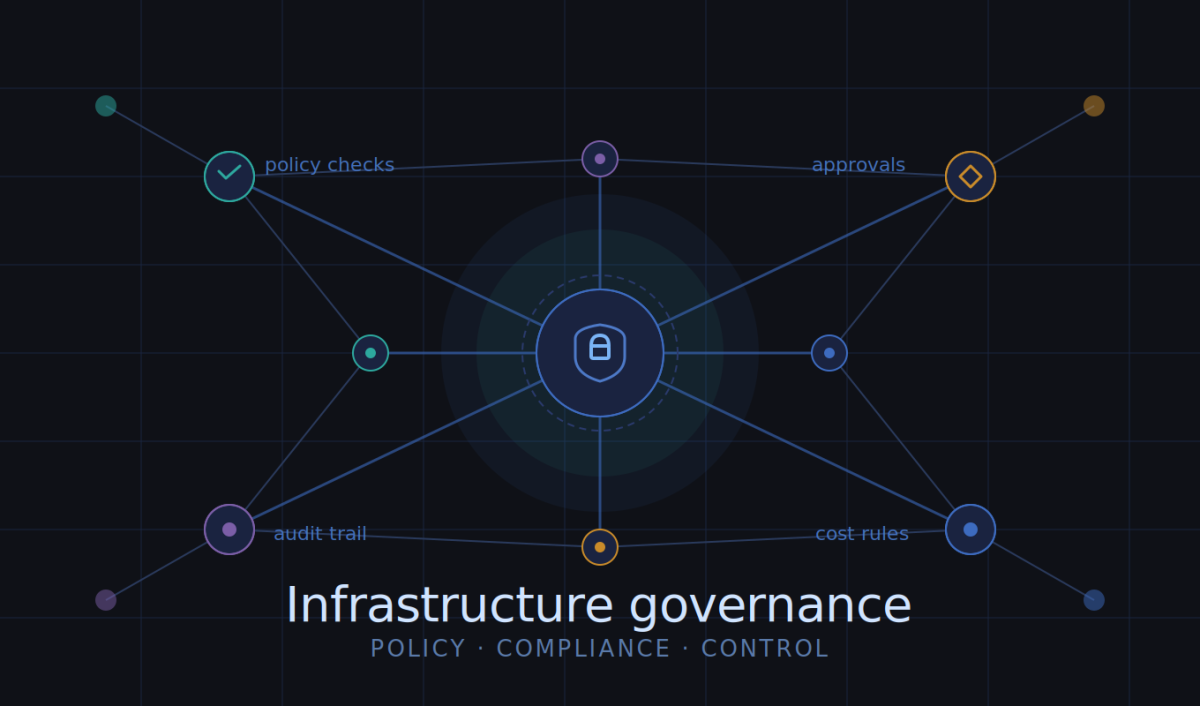
The solution is to apply the same kind of automated controls to infrastructure delivery that software teams have used for years: policy checks, automated plan review, and approval gates.
Policy-as-code lets teams encode rules that every infrastructure change must satisfy before it can be applied. No publicly accessible storage. Required tagging for cost allocation. Approved instance types only. These run automatically in the pipeline, catching violations before production rather than after.
Automated plan review gives teams visibility into the actual impact of a change — what will be created, modified, or destroyed — rather than relying on the engineer’s stated intent. Approval workflows then ensure that high-risk changes get explicit sign-off and a documented justification.
For teams working with Terraform, Spacelift’s guide on Terraform guardrails covers the practical implementation of these controls in detail, including how to layer policy-as-code with CI checks and approval gates without creating bottlenecks for routine work.
Governance as an engineering practice, not an audit exercise
The organizations that handle this well don’t treat infrastructure governance as a compliance checkbox. They treat it as a core engineering practice that makes systems more stable, gives engineers greater confidence when making changes, and makes it easier to answer questions from security and finance leadership when they arise.
That reframe matters because it changes both how the work is prioritized and how well it actually gets done.







